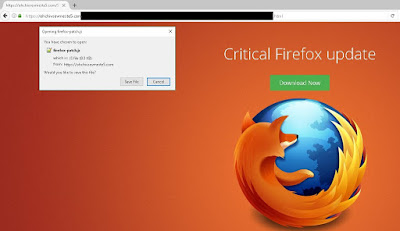
what you get. In this case, a Firefox update is anything but said update.
The domain mentioned in figure 2 is hosted on 192.129.215[.]157, which has a ton of other domains, with most of them appearing random. One of these domains is aiwohblackhatx[.]org, which is registered to a person with email address of abdelrahman.a.y.127@gmail[.]com.
Until recently, that page listed a contact email address as ADMIN@ULTIMATECLIXX[.]COM. This has now been changed, and unfortunately I was unable to take a screen capture at that time.
Ultimateclixx sports a flashing website, promising instant payment:
 |
| Figure 3 - Ultimateclixx website (at time of writing) |
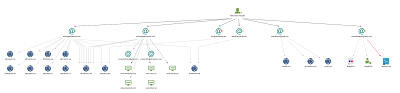
Passive DNS data reveals that the email address mentioned above, has links to other domains, and in particular to a person or persona called 'Mohammed Farajalla'. This persona has multiple email addresses set up, all pointing to click networks:
 |
| Figure 4 - Persona (click to enhance) |
This initially lead me to believe that Abdelrahman and Mohammed are the same person, and is simply an alias. However, WhoIs data from another domain, aifomtomyam69[.]org, reveals a person named 'Abdelrahman Farajallah' as domain owner.
Brothers?
 |
| Figure 5 - Ultimateclix admin forum post (click to enhance) |
Brothers or not, it seems that Mohammed is the 'public face' of the company, and Abdelrahman works in the background, registering domains. A well-oiled business scheme, apparently.
In Figure 5 above, you can see a specific post from 'mhmadfarajalla', hereafter referred to as Mohammed, explaining how he joined
Goldenclixx from 2013 onwards, and made quite some investments. This reply was motivated by a user questioning their legitimacy:
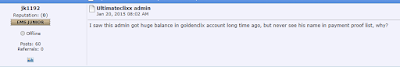 |
| Figure 6 - concerns in regards to the Ultimateclixx admin (click to enhance) |
This was posted in 2015 on the eMoneySpace forum, which is a website created to '
promote or talk about internet money related subjects'. Basically, how to earn money online using ads, which is completely legal.
Link to topic can be found here:
https://www.emoneyspace.com/forum/index.php?topic=361872.0
I've also set up a mirror here:
https://web.archive.org/web/20170918213144/https://www.emoneyspace.com/forum/index.php?topic=361872.0
It appears Abdelrahman and Mohammed have been involved in this scheme for a prolonged period of time. While they may have initially started their project or business as a legitimate way to make money, this has definitely shifted. They are likely located in Palestine. (see also his/their
Twitter account, and make your own deductions.)
The infrastructure
Earlier, I mentioned that domains involved seemed random. Have a look at these domains:
aidixhurricane[.]net
aifomtomyam69[.]org
aingucareersearchings[.]com
aiteobutigim[.]net
aiwohblackhatx[.]org
Notice anything particular? If not, what about the following domains? (includes our initial example)
ohchivsevmeste5[.]com
ohighzapiska[.]org
ohlahlukoil[.]org
ohmuogoodlacksha[.]com
ohseltelists[.]org
To clarify, the 2 first characters are the same for a whole set of domains, while the rest does appear to be (at least semi-)random. Just as a visual aid, here are a few other domains:
vaewedashrecipes[.]net
vahfebankofamerica[.]net
iechow3blog[.]org
iefaxshoeboxapp[.]net
iegiwrealarcade[.]org
iehohclock-world[.]org
iengeluxauto[.]com
ieweimz16[.]org
ieyonthesubfactory[.]net
You may have noticed vahfebankofamerica[.]net in there, it is relatively newly registered (2017-09-12), by a 'Megan Quinn', with email address of qum65@binkmail[.]com. I doubt an actual Ms. Quinn would use this email address. It may try to convince users of its legitimacy, alluding it is part of Bank of America's website. However, nothing could be further from the truth.
Interestingly enough, the domain has hosted a JavaScript at least once, with a familiar pattern:
https://vahfebankofamerica[.]net/3558451080485/150526622449473/firefox-patch[.]js
No doubt this website would also prompt you to download a 'critical security update'. Do I hear redirects mixed with ad or click-fraud and clickjacking? Who doesn't love the smell of that in the morning?
You would not have guessed, but a lot of email addresses seem randomly generated, as well as their personas. Another example includes:
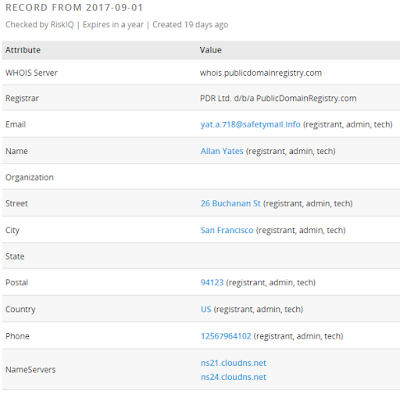 |
| Figure 7 - ohchivsevmeste5[.]com WhoIs info |
Everything in the WhoIs info is fake. Not to say an Allan Yates doesn't exist, but he has nothing to do with any of this - rather he was just unlucky. This may have been the result of a 'fake name generator'.
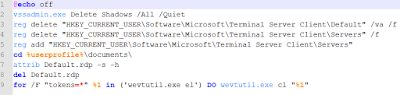
We now have several IP's hosting a bunch of semi-random domains, set up for redirects, ads and likely clickjacking. The initial research started with 192.129.215[.]157, and expanded to/had links to 192.129.215[.]155.
Of course, I decided to take a look at 192.129.215[.]156.
Surprise! It turns out it's just as bad. Maybe we should just block the whole 192.129.215.0/24 subnet?
Some more takeaways from the infrastructure - most of the domains are or have:
- WhoIs Guard Privacy Protection/Privacy Protect:DomainsByProxy;
- Behind CloudFlare;
- A valid SSL cert, issued by Comodo.
What else is there?
Earlier, Mohammed boasted in his forum post about adzbazar.com, one of his new websites, and absolutely 'no ponzi scheme strategy'.
Some of the related websites provided by Mohammed are:
 |
| Figure 8 - adzbazar[.]com |
 |
| Figure 9 - clikerz[.]net |
I think you can start seeing a pattern here.
Circling back, with our email address abdelrahman.a.y.127@gmail[.]com, I noticed another registered domain, adz2you[.]com. You could zay zomeone likez the letter Z. Either way, using PassiveTotal's host pair functionality, we can find a hostpair with
gptplanet. Gptplanet claims to:
Earn money by completing simple tasks online. Everyone can join, it’s absolutely FREE!
As far as I could see, this claim is indeed legit. As far as Mohammed and all his domains go: it didn't take me too long to dig up a forum post with an on-the-point title:
SCAM LEXIADZ ADZBAZAR
Link to topic can be found here:
http://www.gptplanet.com/forum.php?topic=18119
I've also set up a mirror here:
https://web.archive.org/web/20170920001823/http://www.gptplanet.com/forum.php?topic=18119
The topic on gptplanet also references to eMoneySpace, a forum mentioned earlier, and specifically, several topics are set up about 'referral' websites our dear friend Mohammed has set up.
One user made an excellent remark:
It comes to my realize for a whole year now, is that some people are implementing some malicious scripts onto their advertised ad for a user to click on it.
Nail, head, hitting it. It seems that Mohammed isn't done yet however with both scamming people, and infecting users:
 |
| Figure 10 - Offers4all invitation |
There is also mention of another person, 'Agony'. This nickname may refer to Abdelrahman.
Prevention
Prevention in this case is rather short, so here goes:
- Install an antivirus;
- Keep your browser up-to-date;
- Install NoScript if you have Firefox;
- Install a 'well-rounded' ad-blocker, for example uBlock Origin (works with most browsers).
And, where possible, browse the internet with caution.
Note that the campaign on 192.129.215[.]157 remains highly active, and as such, it is recommended to block or blacklist it, as well as the other domains and IPs, provided at the end of this blog post.
Disinfection
When you get a prompt for download or running a 'Firefox patch' similar to above, or any other pop-ups for that matter - where you not instantiated a download yourself - cancel the download or, if not possible, kill your browser's process. This can be done via Task Manager for example.
While I haven't seen any evidence of other malicious behaviour besides ad, click-fraud and clickjacking, it is recommended to:
- Uninstall and reinstall your current browser, along with its extensions;
- Perform a full scan with your installed antivirus product;
- Perform a full scan with another, online, antivirus product, or with Malwarebytes;
- Change your passwords.
Additionally, you may check in your firewall or proxy logs, if there was any connection at some point with any of the domains or IPs provided in the
Indicators
Of
Compromise
section below.
Conclusion
Ad fraud, clickjacking, ad networks, .... There are tons of similar networks out there. While ad networks are usually not malicious, other possibilities exist , such as:
- An ad network is compromised;
- An ad is compromised;
- The ad network is malicious in itself.
Probably, at some point, there should be better security controls for ad networks, in order to prevent an attack or campaign such as the one described in this blog post. Proper security hygiene is necessary for the ad networks, but just as well for any website that serves up ads.
Clickjacking and click-fraud is a common and a very real threat. Are you watching your logs, and acting on them?
IOCs